10 Tips You Need To Know To Secure Your Email
- Email is one of the most common platforms used by users to share sensitive information in the world.
- The convenience of using email has meant that conversations, contacts, and other data are often sent through unsecured channels.
- But Cybercriminals are active to get this information and use it for their own purposes.
Email is the primary means of communication for businesses in today’s world, making it a prime target for cybercriminals. Attacks on organizations’ email systems result in compromised accounts that can damage a company’s reputation and lead to a devastating loss of confidential data. For preventing breaches into your Secure email account follow these ten tips. Make sure you thoroughly understand each point before proceeding. This will help ensure your security sails into the future.
- Secure your email account.
- Use Webmail secure server
- Choose a secure email service
- Take advantage of two-step authentication
- Change your passwords regularly
- Beware of phishing
- Identity Email Phishing Scams
- Don’t click on suspicious links or open attachments in emails you don’t recognize
- Be careful with forwarded emails and other chain letters
- Keep your software up to date
- Encrypt your email messages
- Why you should encrypt your emails:
- How to password protect an email
- How to send encrypted email?
1. Secure Your Email Account
The first and most important thing you need to do is to secure your email account. Passwords are the most common way of securing an email account, and if you use weak passwords, hackers can easily take over your account.
- Use strong passwords that contain a combination of upper and lowercase letters, numbers, and symbols. It’s also a good idea to create unique passwords for each of your accounts. There are many password managers available that can help you keep track of all your passwords.
- Be careful what you click on in emails from strangers or people you don’t know well.
- Don’t open attachments or click on links in suspicious-looking emails—especially those with attachments. They may contain viruses that can harm your computer or steal your personal information, such as usernames and passwords. If you don’t recognize the sender or aren’t expecting an attachment, it’s best to delete such emails immediately.
- Turn off automatic image loading in your email client (i.e., Outlook). Spammers often include images in their messages to track who is opening their emails and reading them, so turning this feature off can help protect your privacy and prevent spamming or hacking.
2. Use Webmail Secure Server
If you want to make sure that your emails are secure, you need to use a secure email server. If your emails are written in plain text, it is easy for anyone else to read them.
If you are using an email server, there will be no way for anyone else to read them. It is a much more secure way of sending emails and it will help to protect your privacy.
Securing your email communications is not a complicated task when you use a secure email server.
The advantages of using a secure email server include
- No risk of “man-in-the-middle” attacks, which can lead to sensitive information being exposed on the Internet or intercepted by third parties.
- No risk of having emails read while they are being stored on the email server.
- No risk of emails being read while they are in transit to their destination.
You can send and receive encrypted emails with anyone, even if they do not use a secure email server themselves. The encryption keys that are used to encrypt emails and decrypt the messages are always stored securely by the Secure Email Server vendor.
3. Choose a Secure Email Service
Use a secure web-based email service such as ProtonMail, Tutanota, or StartMail that supports end-to-end encryption.
End-to-end encryption means that only the person sending and receiving the email can read it. The email provider itself cannot access the contents of your emails.
These services also store all emails on servers located in jurisdictions with strong privacy laws to prevent governments from snooping on their users’ inboxes.
Be aware that these services have limited free tiers, and they require you to pay to use their services at full capacity.
4. Take Advantage of Two-Step Authentication
Two-step authentication is a more secure way to log in to your email account by adding another layer of security. When you set up two-step authentication, you’ll need to enter more than just your password to sign in.
You’ll be asked for an extra code or password that only you would know. This helps protect your account if someone knows your password.
You can find two-step authentication in the security settings of most major email providers. Once you’ve enabled two-step authentication, you’ll be prompted to set up a second login option, such as a phone number, Google Authenticator, or Authy app for smartphones.
Despite all the advancements in security, email remains vulnerable to hackers. Fortunately, there are several things you can do to protect your email account from hacking.
5. Change your Passwords Regularly
Change your password regularly – at least once every two months – and make sure it is strong and unique for each of your online accounts.
A strong password should be a lengthy combination of letters (upper-case and lower-case), numbers, and symbols that are difficult to guess.
It’s also a good idea to have different passwords for each of your accounts. If a hacker gets hold of one password they needn’t necessarily get access to all of them.
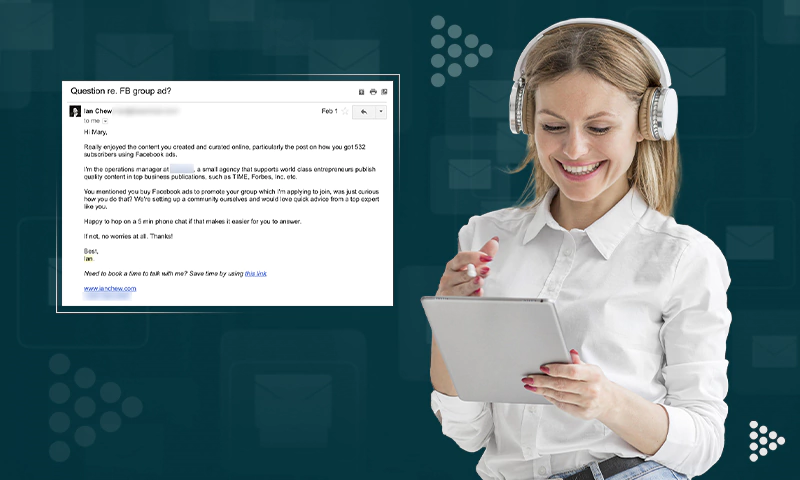
6. Beware of Phishing
To keep your email address secure is to avoid clicking on links in emails that you are not expecting. If you get an email from a company you do business with and it contains a link, or an attachment, or asks you to log into your account, call the company. Do not use the phone number in the email. Go to their website and get their customer service phone number from there.
If you are unsure whether an email is legitimate, call the company first and ask about it.
Identify Email Phishing Scams
Phishing scams often come from people pretending to be someone else. They may say they are from your bank or credit card company asking for information about your account. Or they could be pretending to be from a government agency like the IRS asking for personal information.
Most of these phishing scam emails will contain some alarmist message about how you need to act immediately, or something bad will happen.There is usually some type of “click here” link that takes you somewhere where they try to steal your information.
7. Don’t Click on Suspicious Links or Open Attachments in Emails You Don’t Recognize
Phishing scams have become a popular way for attackers to access your personal information. A phishing scam is an attack that uses emails with links or attachments to spread malware such as viruses, worms, and ransomware.
If you receive an email from someone you don’t recognize, do not click any links or open any attachments. This could be a phishing attempt in which the attacker hopes that you’ll fall for the scam and click on the link or attachment, thereby allowing them access to your computer or personal information.
8. Be Careful with Forwarded Emails and Other Chain Letters
It’s a well-known fact that the Internet is full of scams, but you may not know just how dangerous it can be to forward emails and chain letters.
When you forward an email or a chain letter, you are sharing your contacts with strangers. Those strangers may sell or use your contacts for any number of purposes. They could send you viruses or spam emails. They could even sell your contacts to other companies.
If you receive an email from someone you trust that asks you to forward it to all of your contacts, think twice before complying with the request. It’s far better to cut and paste the message into a new email than it is to hit “forward.”
If one of your friends forwards an email to you that asks you to provide your personal information, stop and think about what is being asked of you. If it’s something like an “Internet scavenger hunt,” then don’t do it. Do not provide any personal information over the Internet unless it’s through a secure website that has been recommended by someone you trust.
9. Keep Your Software Up To Date
This is a simple step, but it’s the most important. Any software you use on your computer — your web browser, email client, word processor, and so on — needs to be updated whenever new versions are available. Software developers typically fix bugs with updates and patch security vulnerabilities, so missing out on an update can expose you to unnecessary risk.
Make sure you know how to check for updates and install them. With Windows, you can set it to do that automatically; with Macs, you can also set it to automatically install system updates (though not app updates). With Linux, some distributions make this easy; others don’t.
If you’re using a smartphone or tablet, the same rule applies: Make sure all of your apps are updated as soon as possible.
10. Encrypt Your Email Messages
These days, everybody is talking about the security of their emails and how to make their email messaging more secure.
Email encryption ensures that only the intended recipient can read your email messages. Encrypted messages can be sent to anyone with an email address — even someone who doesn’t use a service that supports end-to-end encryption.
But not every email service supports encryption and not every message you send needs to be encrypted. Fortunately, there are ways to encrypt individual messages without switching services or changing email addresses altogether.
Why You Should Encrypt Your Emails
If you’re looking for an easy way to keep messages secure, encrypted email is a great place to start. Encrypted emails are harder to intercept and read by unauthorized users or hackers than unencrypted ones. You can use encryption if you’re worried about someone spying on your communications — including government agencies and advertisers.
How to Password Protect an Email
If you’re sending an email that contains sensitive information, you might want to password protect it. This is especially important if you’re using an email service provider that doesn’t have end-to-end encryption, a safeguard that prevents your emails from being read by anyone but the intended recipient.
There are two ways to password protect an email: using a third-party website or encrypting the message with Microsoft Outlook.
To password protect an email through a third-party site:
1. Use a website such as Lockbin or Encryptomatic’s OpenPGP to encrypt your message. You’ll first need to create an account on the service and then input the sender’s and recipient’s names and email addresses.
2. Compose your message and include any attachments as usual. Then, click Send Secure Email. The recipient will receive an email with a link to access the secure message centre. They’ll be prompted to enter a passcode (the one you created) to view the email and its contents.
Microsoft Outlook includes a feature that allows you to protect your email messages before sending them. With this option enabled, the recipient of your message will be required to enter a password you define before being able to read the contents of the message. This can be useful if you are sending confidential information via email and want to make sure it is only readable by the intended recipient.
- Compose a new message in Outlook.
- Enter the recipient’s email address in the To field
- Click Options
- Select More Options in the dialog box that appears
- In the next dialog box, click the Security Settings button
- Make sure Encrypt Message Contents and Attachments is checked and click OK (you will not be prompted for a password at this time)
- The Encrypt button will appear in your message window (see screenshot below) — click it, then enter a password for your encrypted message (write down this password — you will need to provide it to anyone who receives an encrypted message from you). Click OK when finished.
Note: If you want to use this feature, both you and the person receiving your email need to have an account with Microsoft Outlook.
What Is A Privacy Email?
A privacy email is an email address that is used to protect your real identity.
The most common uses of privacy emails are
- Preventing spam from getting into your personal inbox
- Managing a large number of accounts from one place.
A privacy email can be accessed via webmail, an email client, or by forwarding the emails to another address.
How to Send Encrypted Email?
Hackers are very interested in stealing email passwords. However, there are ways to hide the contents of your email messages and make it more difficult for an attacker to read what you’re sending.
You can use one of these methods to send encrypted email messages:
1) Use PGP/GPG encryption. This is a public-key encryption system that uses two keys: one public and the other private. Anyone with the public key can encrypt emails sent with that key. The recipient must have the private key to decrypt those emails. Two-factor authentication can also help prevent unauthorized access to your account.
2) Use S/MIME or PGP to encrypt text messages and emails. These are older/less secure versions of PGP/GPG but are still useful as a way to send encrypted text messages or emails, especially if you’re concerned about privacy issues.
Takeaway: The most important thing is to always be aware that security threats exist and take the proper steps to protect yourself against them as well as be proactive when it comes to avoiding viruses, malware, etc.
FAQs
Ans: Email security is the means by which a user is able to protect the content of his email, as well as his email accounts, from being hacked by unauthorized third parties.
Email security is a highly important factor in today’s world. With more and more business being conducted over email, it has become more common for criminals to target emails in order to steal sensitive information or even money. Because of this threat, many businesses have begun implementing email security policies and procedures in order to keep their data safe.
Ans: Without proper email security, you could lose sensitive data or let hackers into your systems. At an individual level, this could mean identity theft. At a business level, it could mean financial loss or legal consequences.
Ans: Email security is a broad term that refers to a variety of tools and techniques used to protect email. It encompasses everything from the basic practices of avoiding phishing and spam to high-level encryption and digital certificates.
the most common types of email security include:
- Encryption
- Authentication
- Filtering
Ans: Encryption is the process of turning plain text into a scrambled form that only authorized parties can read. When email messages are encrypted, they can only be decrypted by those with the right key or password. Encryption is particularly important in healthcare settings, where personal information must be protected by law.
Ans: Authentication is the process of ensuring that users are whom they say they are. Authentication helps ensure that only authorized users are able to access sensitive data such as emails and documents.
Ans: It’s important to secure your email accounts because if someone gets access to your email account, they can potentially get access to a lot of other accounts you own.
In particular, many websites use the “forgot my password” feature to send you a new password. If someone breaks into your email account, they can break into many other accounts simply by choosing the “forgot my password” feature. In addition, someone who breaks into your email account will see everything you have ever sent or received via that address.
Email security is not just an add-on to your email software; it’s an essential element of your cyber security strategy and part of a holistic approach to protecting your business. It’s designed to work alongside, not instead of, your other security systems.
Ans: To date, the most secure email services are Hushmail and ProtonMail. Both email services offer end-to-end encryption. This means that messages are encrypted from the point of origin to the point of destination. This acts as an extra layer of security as even if a hacker intercepted the message, it would be indecipherable without a decryption key.
Hushmail and ProtonMail both require users to enter passwords that are used to encrypt messages before they are sent and decrypt them when they are received. Hushmail also makes use of public-key cryptography with its encryption process.
Ans: DMARC (Domain-based Message Authentication, Reporting & Conformance) is an email authentication protocol that protects against domain spoofing by verifying that incoming mail from a domain matches certain policies set forth by the domain owner. DMARC can prevent these attacks from happening before they ever reach your inbox.
Ans: DMARC allows you to tell other mail servers what to do if they receive an email that appears to originate from your domain but fails authentication checks like SPF or DKIM. Setting up a DMARC policy gives you more control over how mail servers handle unauthenticated messages and provide additional visibility into the unauthorized use of your domain through reporting.
Share