How to Detect a Phishing Email

Cyber-attacks have become one of the biggest threats targeting the world today. Everyone is in danger of becoming a victim, whether it is an individual, big or small business, or even a government. The loss from the reported fraud cases has come up to 42 billion dollars, and the number constantly keeps growing. Worst of all, there are still many unreported fraud cases that would add significantly to that number.
There are so many different types of fraud that can affect just about anyone, especially through email. But, out of them, the most upsetting one is a phishing attack as it directly exploits people’s natural tendency to trust. While we might be able to accept the attacks due to security weaknesses in the technology surrounding us, being directly targeted and causing an attack is a harder pill to swallow. However, there are many ways of fighting fraud as per SEON’s fraud detection and prevention guide.
What Exactly is a Phishing Attack?
Phishing is one of the most common types of attacks and one of the favorite ones for cybercriminals as it can bring the most significant gain with a little effort. Forbes claims the effect of phishing attacks and that they are responsible for more than 80% of reported security incidents. Phishing happens when cybercriminals send malicious emails trying to trick people into revealing sensitive information. They do this by tricking individuals into believing that fraudsters are legitimate and trustworthy sources. This makes people more inclined to provide sensitive and confidential data such as financial information, system credentials, intellectual property, or other sensitive data. While phishing is not a new phenomenon, it is becoming more and more widespread, making it more critical than ever to know how to detect and prevent a phishing scam. Regardless of which email service provider you use, the threat is real, and the same detection strategy will apply to all of them.
How to Recognize a Phishing Email?
There is hardly anyone who hasn’t received a spam or phishing email. Your email provider is usually really good at filtering them, and we have all developed tips to flag spam attacks and to recognize them. But, in recent years, phishing emails have become more sophisticated, making it harder to detect them at first glance. Luckily, these are still ways of detecting a phishing email that can help you prevent the attack.
1. Emails Demanding an Urgent Action
Fraudsters will try to pressure you to action by detailing negative outcomes that can happen if you don’t respond immediately. They do this, so you won’t think you have enough time to research the email and notice any inconsistencies. If the email contains any type of threat or urgent request, you should consider that a red flag and investigate it more closely.
2. Bad Grammar and Spelling Errors
Most businesses will have spell-checking software to ensure all outgoing emails are grammatically correct, which means emails that are coming from legitimate sources won’t have grammar or spelling mistakes.
3. Unusual Request
If the request you received in the email is uncommon, such as your boss requesting an urgent money transfer or asking for the bank account details, you need to consider it as a red flag. Always double-check this type of email by confirming the request with another communication method. It is better to be safe than sorry.
4. Unfamiliar or Strange Greeting
Another area you should keep an eye on when receiving an email is the greeting. For example, receiving an email from a financial institution calling you “Dear” or your family member greeting you formally could indicate a fraudulent attempt.
5. Asking Confidential Information
Any email that demands Login information, payment or financial details, or any other confidential information should be considered suspicious and treated as such. Never click a link from the email; always go through your browser and input the website in question by yourself.
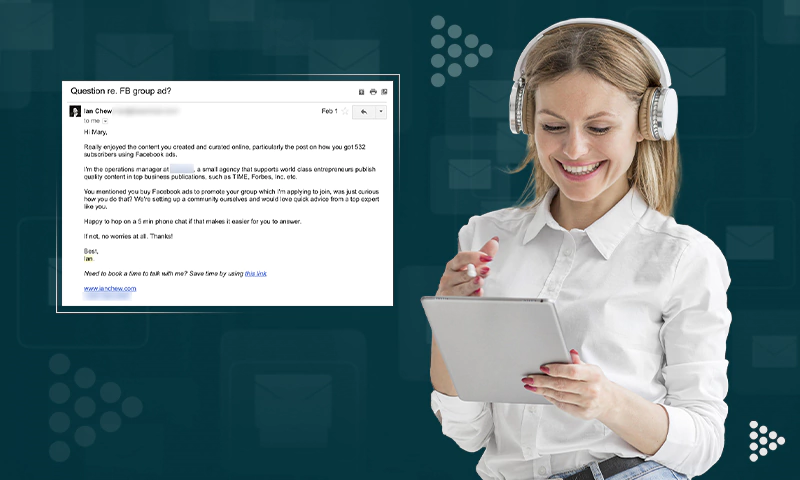
6. Discrepancies Between the Email Address, Link, and Domain Name
Any discrepancy should always be investigated, such as receiving an email from your CEO but from a completely different email address or email from a specific company, but the link or domain name is for something completely different.
Share